What Is Penetration Testing and Why Does Your Business Need It?
By Oakstone Security Group
April 18, 2025
Your systems have never been more exposed. Every application you run, every network you operate, and every device connected to your infrastructure is a potential entry point for an attacker. The question is not whether vulnerabilities exist. They do. The question is whether you find them first.
What Penetration Testing Actually Is
Penetration testing is a deliberate, authorised attempt to compromise your systems using the same techniques a real attacker would use. A qualified tester does not run a scanner and hand you the output. They think like an adversary: probing for misconfigurations, chaining together small weaknesses into meaningful attack paths, and demonstrating what a motivated attacker could actually achieve if they set their sights on you.
This distinction matters. Automated vulnerability scanners are useful tools, but they produce long lists of theoretical issues with no sense of priority or real-world impact. A penetration test produces something different: evidence. Evidence of what is exploitable, how it could be exploited, and what the consequences would be.
The OWASP Foundation and the Penetration Testing Execution Standard both provide frameworks that define what rigorous penetration testing looks like. Oakstone works in accordance with these standards on every engagement.
Why It Matters
The cost of discovering a vulnerability during a penetration test is a fixed, predictable professional fee. The cost of discovering the same vulnerability during a breach is not. The IBM Cost of a Data Breach Report has consistently found that the average cost of a data breach runs into the millions of dollars once incident response, legal exposure, regulatory penalties, and reputational damage are accounted for.
Beyond the financial case, penetration testing provides something harder to quantify: an honest picture of where you stand. Security investments are often made on the basis of assumption rather than evidence. A penetration test replaces assumption with fact. It tells you which controls are working, which are not, and where your money is best spent next.
For businesses subject to compliance requirements under frameworks such as PCI DSS, ISO 27001, or SOC 2, regular penetration testing is not optional. It is a condition of maintaining certification. But the businesses that get the most value from penetration testing are those that treat it as a genuine security exercise rather than a box to tick.
Network Penetration Testing
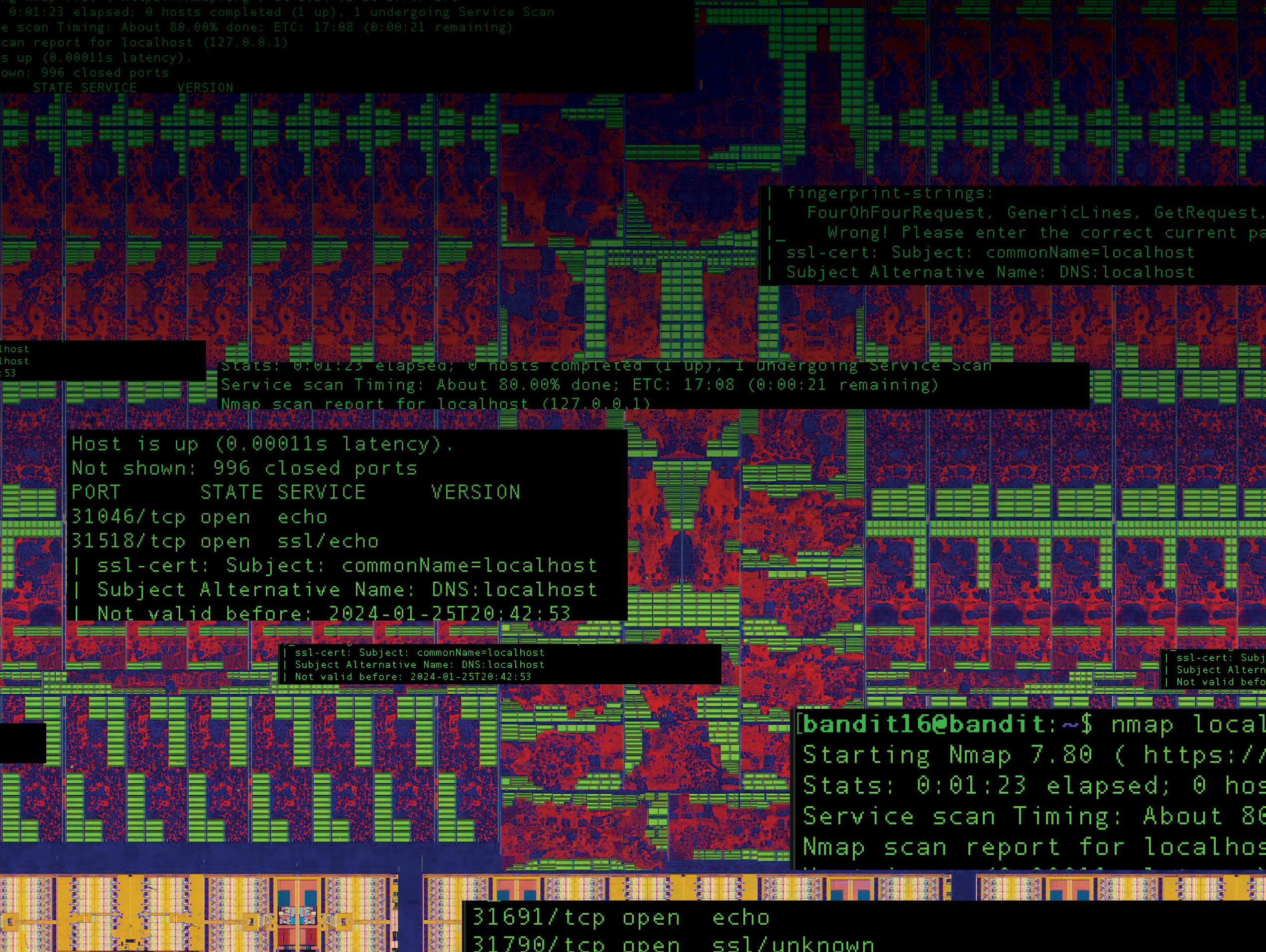
A network penetration test examines the infrastructure that underpins your operations: firewalls, routers, switches, servers, and the services exposed on them. The objective is to identify paths an attacker could use to gain unauthorised access, escalate privileges, or move laterally through your environment.
Common findings in network assessments include exposed management interfaces, weak or default credentials on network devices, unpatched systems with known exploitable vulnerabilities, and overly permissive firewall rules that allow traffic that should never be permitted. Each of these is a known category of failure that attackers actively exploit, and each is routinely found in environments that believe themselves to be well-secured.
External network testing examines what is visible and accessible from the internet. Internal testing examines what an attacker could do once inside your perimeter, whether through a phishing attack, a compromised workstation, or a malicious insider. Both perspectives are necessary for a complete picture.
Web and Application Penetration Testing
Web applications are among the most commonly exploited entry points into an organisation. They are complex, frequently updated, and directly internet-facing. Every feature added to an application is a potential attack surface.
Web and application penetration testing examines how an application handles authentication, session management, input validation, access control, and the handling of sensitive data. Testers look for vulnerabilities such as SQL injection, cross-site scripting, insecure direct object references, and broken authentication flows — categories documented in the OWASP Top 10, which represents the most critical and commonly exploited application security risks.
Beyond the technical vulnerabilities, application testing also examines business logic: the ways in which an application can be manipulated to behave in ways its developers did not intend. These vulnerabilities are invisible to scanners and require a tester who understands how the application is supposed to work and can reason about how it might be abused.
What You Get at the End
Every Oakstone engagement concludes with a detailed report that reflects the actual findings of the test, not a reformatted scanner output. The report contains:
An executive summary written for decision-makers who need to understand the business risk without wading through technical detail. This section describes what we found, what it means, and what to do about it.
Detailed technical findings, each documented with a description of the vulnerability, the evidence demonstrating exploitability, a risk rating, and specific remediation guidance. Findings are prioritised so that your team knows what to address first.
A remediation roadmap that translates the findings into a sequence of actions aligned with risk rather than effort. Not every finding carries the same weight, and the report makes that clear.
We do not pad reports with low-quality automated output to make them look more substantial. Every finding in an Oakstone report was verified manually. If it is in the report, it is real.
Why Oakstone
There is no shortage of firms that will take your money and return a report. The question worth asking is whether the report will tell you something true and useful.
Oakstone approaches every engagement as an adversary would. We are not looking for what a scanner finds. We are looking for what a motivated attacker would find if they had time, capability, and a specific interest in your organisation. That mindset produces different results.
We are also committed to communication throughout the engagement, not just at the end. If we find something critical during testing, you hear about it immediately. You do not wait for the final report to learn that you have a serious problem.
Our engagements are scoped carefully at the outset. We do not use scope as a way to limit liability. We use it to ensure that the test addresses the areas of genuine risk for your specific environment. What is in scope and what is not is agreed in writing before any work begins, and any deviation requires your explicit authorisation.
When to Test
If you have not had a penetration test in the last twelve months, you are overdue. If you have recently deployed a new application, made significant changes to your infrastructure, or experienced a security incident, you should test before you consider yourself clear.
Penetration testing is most effective as a regular practice rather than a single event. Environments change. New vulnerabilities emerge. Remediations sometimes introduce new weaknesses. The value of testing compounds over time as it becomes part of how you manage security rather than an occasional exercise.
To discuss scoping an engagement or to ask questions about what testing would look like for your environment, contact Oakstone.